As you might have seen in the last couple of days, there are huge news about some security bugs in CPUs from different vendors (not just intel). The Microsoft Security Response Center released a PowerShell Module on the PowerShell Gallery called SpeculationControl, which verifies if your system is protected or not.
Microsoft is aware of a new publicly disclosed class of vulnerabilities that are referred to as “speculative execution side-channel attacks” that affect many modern processors and operating systems, including chipsets from Intel, AMD, and ARM.
Note This issue also affects other systems, such as Android, Chrome, iOS, and MacOS, so we advise customers to seek guidance from those vendors.
Microsoft has released several updates to help mitigate these vulnerabilities. We have also taken action to secure our cloud services. See the following sections for more information.
Microsoft has not yet received any information to indicate that these vulnerabilities have been used to attack customers. Microsoft continues working closely with industry partners including chip makers, hardware OEMs, and app vendors to protect customers. To get all available protections, hardware/firmware and software updates are required. This includes microcode from device OEMs and, in some cases, updates to antivirus software as well.
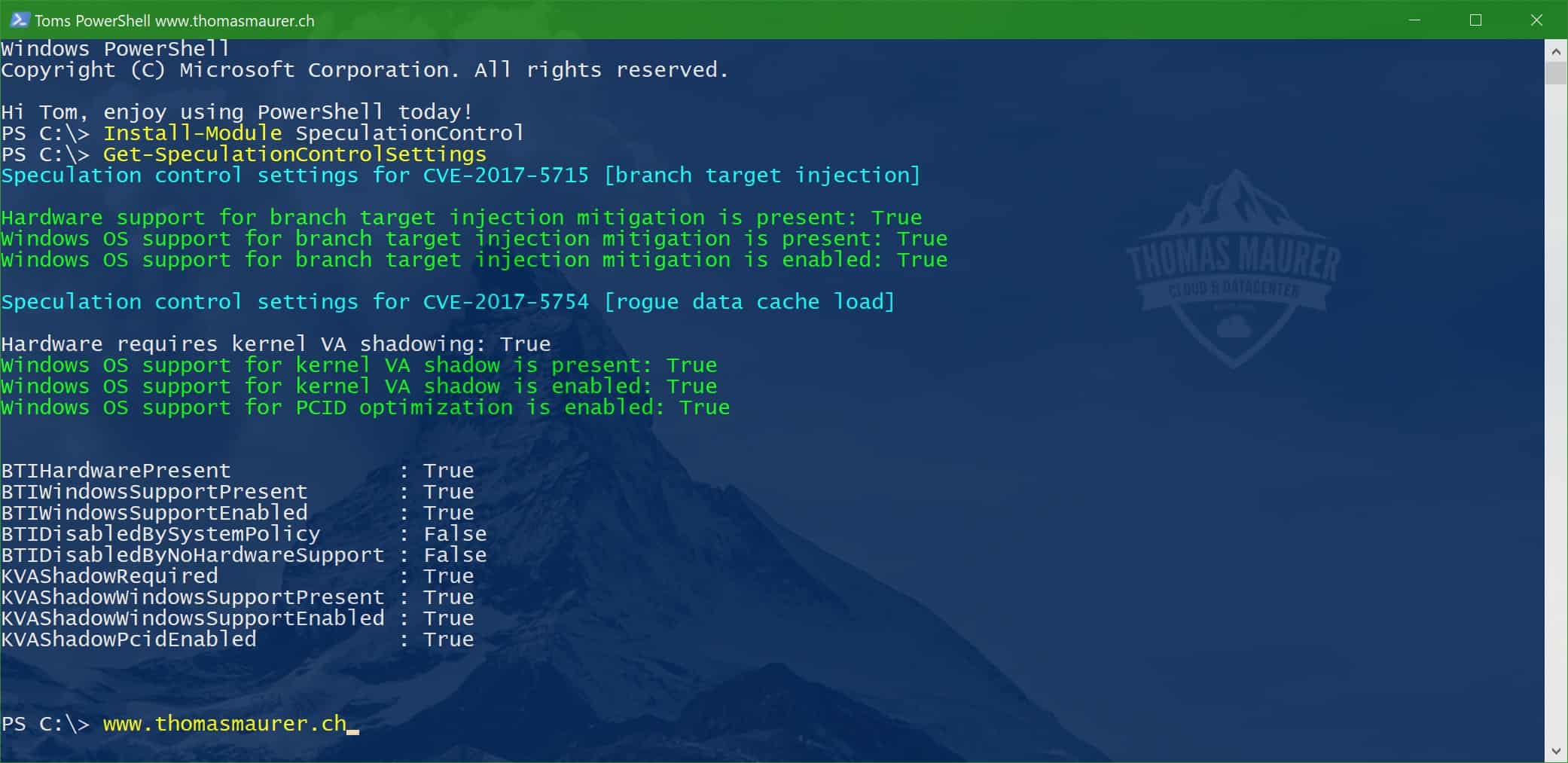
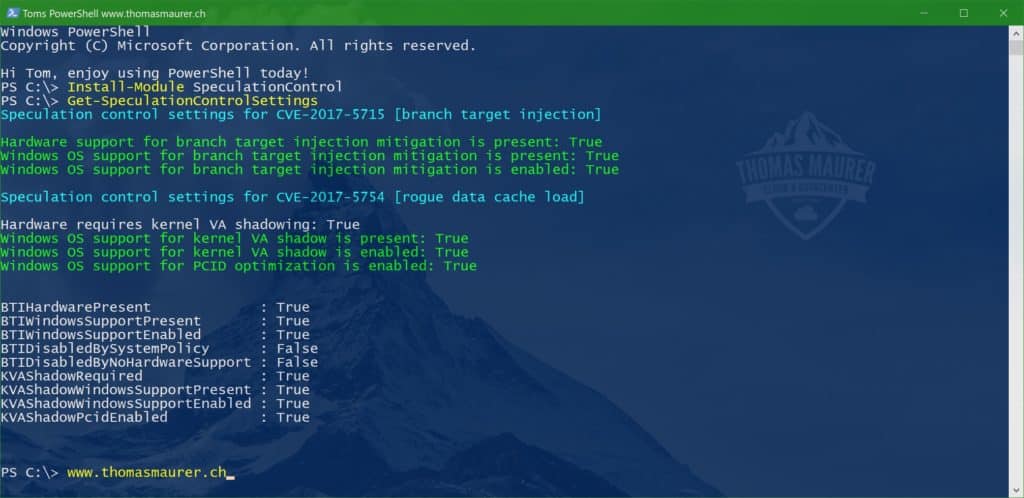
# Install the PowerShell module Install-Module SpeculationControl # Run the PowerShell module to validate protections are enabled Get-SpeculationControlSettings
Enabled protections will show in the output as “True” like in this screenshot here
So make sure you patch your systems, for Windows and Windows Server are already patches available and the Surface Familiy already got some firmware updates.
Also check out Mike F Robbins (Microsoft MVP) how he explains how to use the SpeculationControl PowerShell module on remote machines.
Tags: Chipset, CVE-2017-5715, CVE-2017-5754, Intel, Meltdown, Microsoft, PowerShell, Spectre, SpeculationControl, vulnerabilities, vulnerability, Windows, Windows 10, Windows Server Last modified: January 7, 2019








I’m hoping we can leverage this module to create a CI in ConfigMgr to allow us to report on our update progress. Not sure if I’ll have time myself in the next couple of days, so I’m watching my Twitter feed closely in case someone else blogs about something like that.
Do not worked for me. I see a error.
hi Thomas
i get an information, that the repository is not trusted.
“PSGallery”
If you have not tursted the PSGallery, you can run the following to temporary run the Module:
Install the PowerShell Module
PS> Install-Module SpeculationControl
Run the PowerShell module to validate the protections are enabled
PS> # Save the current execution policy so it can be reset
PS> $SaveExecutionPolicy = Get-ExecutionPolicy
PS> Set-ExecutionPolicy RemoteSigned -Scope Currentuser
PS> Import-Module SpeculationControl
PS> Get-SpeculationControlSettings
PS> # Reset the execution policy to the original state
PS> Set-ExecutionPolicy $SaveExecutionPolicy -Scope Currentuser
Hi thanks for your info.
I seem to be unable to patch Hyper-V Server 2012R2 (aka “core”)
I add the Antivirus regkey in order for WU to “see” KB4056895 but after installing and rebooting I am met with “…we couldn’t complete the updates undoing the changes…”
Same thing if I try to manually install this or KB4056898.
Maybe you have some comment or suggestion or I guess I need to dig in logs.
Thanks!